
The Resolv hack: $25M from a single compromised key
At 02:21 UTC on March 22, a security exploit converted $200,000 in USDC into approximately $25 million. The breach involved a compromised private key with unlimited minting privileges, allowing for the issuance of 80 million unbacked USR tokens. This resulted in a 97.5% collapse of the stablecoin’s value in under 20 minutes. Significant losses are currently being assessed across all lending protocols that accepted USR or wstUSR as collateral.
Resolv’s USR is a delta-neutral stablecoin: users deposit USDC and a privileged off-chain service authorizes minting by signing a transaction specifying how much USR to issue. The vulnerability was that the minting contract’s only validation was signature verification, if you had a valid signature, you could mint any amount. No collateral ratio check, no epoch cap or no circuit breaker.
The attacker obtained the private key, which was hosted on AWS infrastructure as a single EOA with no multisig, and used it to authorize two mints:
Mint 1: 100,000 USDC deposited → 49,950,000 USR issued
Mint 2: ~30,000,000 USR minted minutes later
The effect was ~80 million unbacked USR, against a legitimate circulating supply of ~100 million. The attacker sold through Curve, KyberSwap, and Velora, converting to USDC/USDT and then to approximately 9,100–11,400 ETH (~$24–25M). USR hit $0.025 on Curve at 02:38 UTC, a 97.5% depeg, 17 minutes after the first mint.

Source: Geckoterminal
Resolv had completed 14+ audits across five firms and maintained a $500,000 Immunefi bounty. None of them flagged the unbounded mint path since the root cause, a single EOA with unlimited minting authority and no on-chain bounds, is an architectural decision and not a code bug. Auditors share some responsibility here, but the primary call was made by whoever designed the system that way.
Resolv confirmed the underlying collateral pool was not touched. The exploit hit the minting layer instead of the backing assets. The practical consequence is that the real assets are still there, but they now back ~180 million USR instead of ~100 million.
RLP is Resolv’s junior tranche is designed to absorb first-loss on collateral-side events like negative funding rates or exchange failures. Whether a supply-inflation attack falls within that mandate is unclear at the moment, and it is likely to be resolved through governance or legal process rather than the protocol itself.
Cascade Into Lending Markets and Curators
The 17-minute crash of wstUSR and RLP created bad debt across Fluid, Venus, and some specific markets on Morpho, and Euler. In some protocols oracles relied on redemption prices rather than market rates, while in others the speed of the crash prevented liquidations. On Morpho, the Public Allocator’s automated rebalancing, designed to shift liquidity toward high-demand pools, responded to utilization spikes caused by arbitrageurs borrowing USDC against mispriced collateral. While this logic intended to optimize capital efficiency, the rapid shift resulted in a ~$6M loss for the Gauntlet USDC Core vault before intervention. Other curators including Re7, KPK, MEV Capital, Clearstar, August, and Tulipa Capital, saw impacts under $1M. Fluid’s oracles updated but the velocity of the move similarly prevented liquidations
Recovery: where things stand
Resolv Labs completed $77M in USR redemptions for whitelisted wallets, covering more than 90% of the affected user group. A second phase addresses the remainder. On the token side: 9M USR were burned on the day of the hack. After a 72-hour governance timelock, a required delay to give the community time to review the contract upgrade before it executed, addresses linked to the attacker were blacklisted, freezing an additional 36M USR. In total, 46M USR (57% of the illicit supply) has been frozen. The remaining ~34M USR is not accounted for. Resolv has not disclosed what happens to those tokens.
Fluid reported repaying approximately $70M in USR-related debt by March 25, with funding sourced in part from Cyber Fund and Jupiter. Fluid has committed to full user compensation. Resolv protocol itself remains paused. No formal post-mortem has been published yet.
Disclaimer: The information provided in this newsletter is for educational and informational purposes only and does not constitute financial, investment, or legal advice.
Key Weekly DeFi Metrics
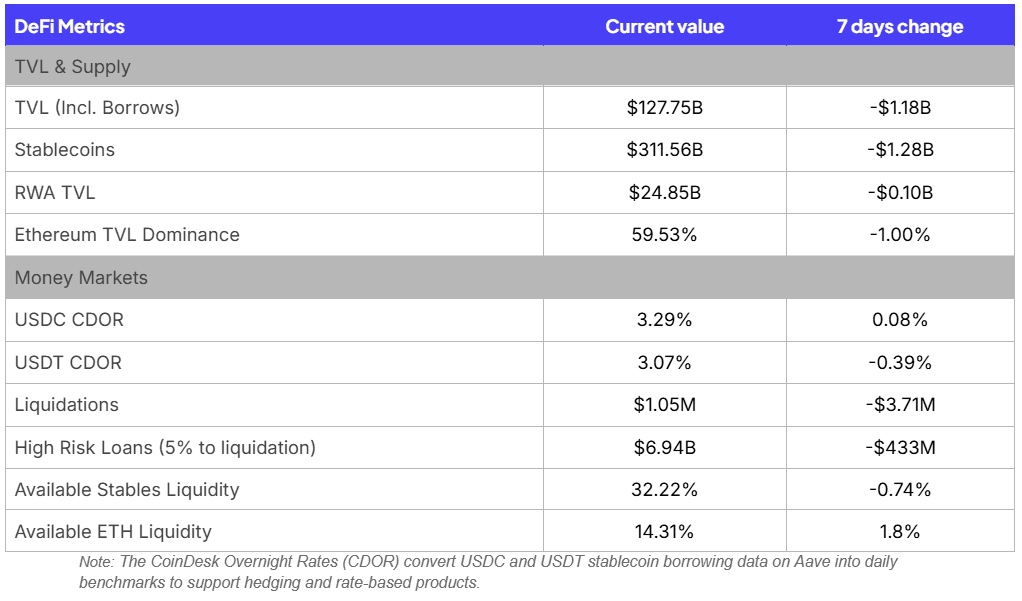
Key takeaways for this week:
The Resolv exploit has had a ripple effect through the market with TVL and Stablecoins supplies the most affected, resulting in -$1.18B and -$1.28B decreases, respectively.
Liquidations have dropped to $1M as users derisked to avoid Resolv contagion, but note that liquidations would have been much higher if markets would have been able to liquidate against Resolv assets correctly
Evaluating Curators Through Best Practices and Transparency
In modular decentralized finance, the risks highlighted by events like the Resolv (USR) depeg, where slippage and oracle failures led to significant market stress, demonstrate that protocol-level neutrality does not guarantee safety. Instead, the responsibility for vault performance and security rests with the curator, who defines investment strategies, selects collateral, and calibrates liquidation parameters. Standard practice involves tiering assets by liquidity and volatility, ensuring that conservative Liquidation Loan-to-Value (LLTV) ratios provide a necessary buffer against the types of systemic shocks observed in recent market cycles.
Curator Transparency and Reporting Standards
Curators maintain trust through clear transparency and reporting that extends beyond basic dashboards to include detailed asset-level analysis. The diversity of these strategies is reflected in the composition of collateral assets, where curators balance between blue-chip exposure, yield-bearing stables and exotics.
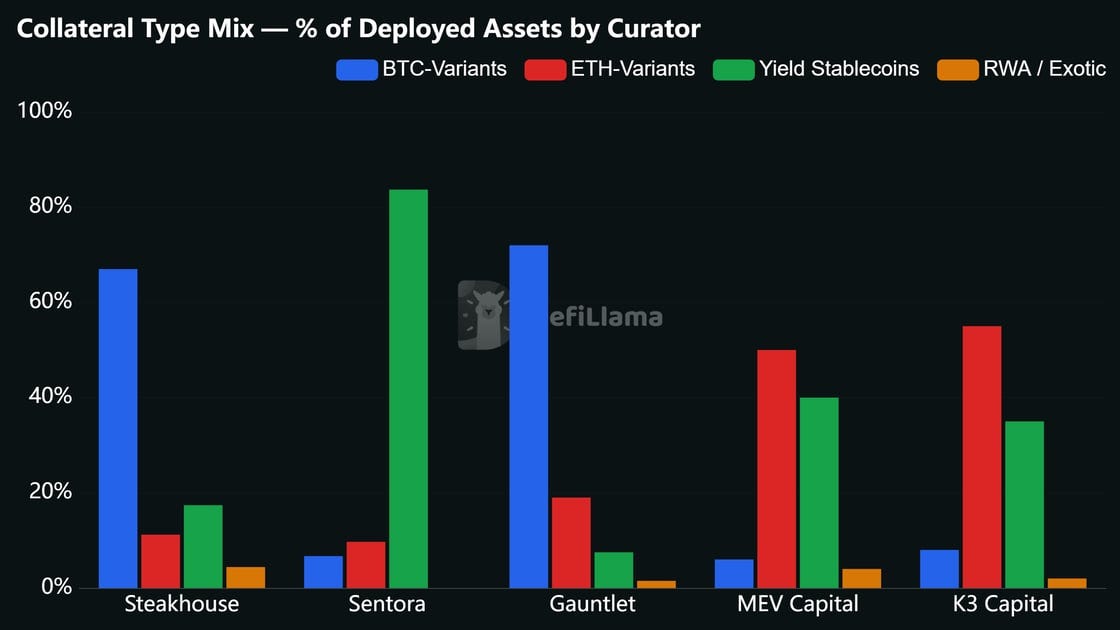
Source: DeFiLlama
Collateral Tiering: Separate assets into risk categories to maintain vault hygiene. Onboarding reports should document technical, oracle, and liquidity risks for every new collateral type.
Parameter Justification: Provide clear rationale for LLTVs and supply caps based on historical volatility and DEX liquidity. Higher-risk assets require more conservative thresholds.
Real-time Reporting: Public dashboards should display Capital at Risk (CaR), Value at Risk (VaR), and utilization levels to verify alignment with the vault’s stated mandate.
Governance and Incidents: Use emergency roles like Sentinels and enforce timelocks for all changes. Incident post-mortems are essential to demonstrate risk management maturity.
User Due Diligence and Considerations
For users and institutional allocators, selecting a vault is a function of “Know Your Curator” (KYC) rather than protocol-level trust. Due diligence should focus on the operational and strategic integrity of the management layer.
OpSec and Timelocks: Verify the curator’s governance setup and ensure enforceable timelocks are in place to allow withdrawals before risk-increasing changes take effect.
Oracle Health: Identify if assets use decentralized feeds, TWAPs, or hardcoded oracles. Users should recognize that oracle choice dictates how price divergence is handled.
Track Record and Liquidity: Review the curator’s historical bad debt record and ensure the vault maintains an “idle” balance to facilitate withdrawals during high-utilization periods.
Curation is a complex undertaking performed in a highly dynamic environment where market conditions and asset profiles evolve rapidly. By adopting standard practices in transparency and due diligence on both the curator and user sides, participants can improve the overall health of lending markets. These collective efforts increase the resiliency of the entire ecosystem against systemic shocks.







