
This issue focuses on what changed in the last seven days, how this synthetic contagion infected the broader composability stack, and what it implies for risk managers, infrastructure providers, and institutional allocators. The core question is no longer how to blindly maximize composable yield, but how to engineer strict structural isolation against systemic tail risks without sacrificing capital efficiency.
Ecosystem Stress Test: The Kelp DAO Contagion & "DeFi United"
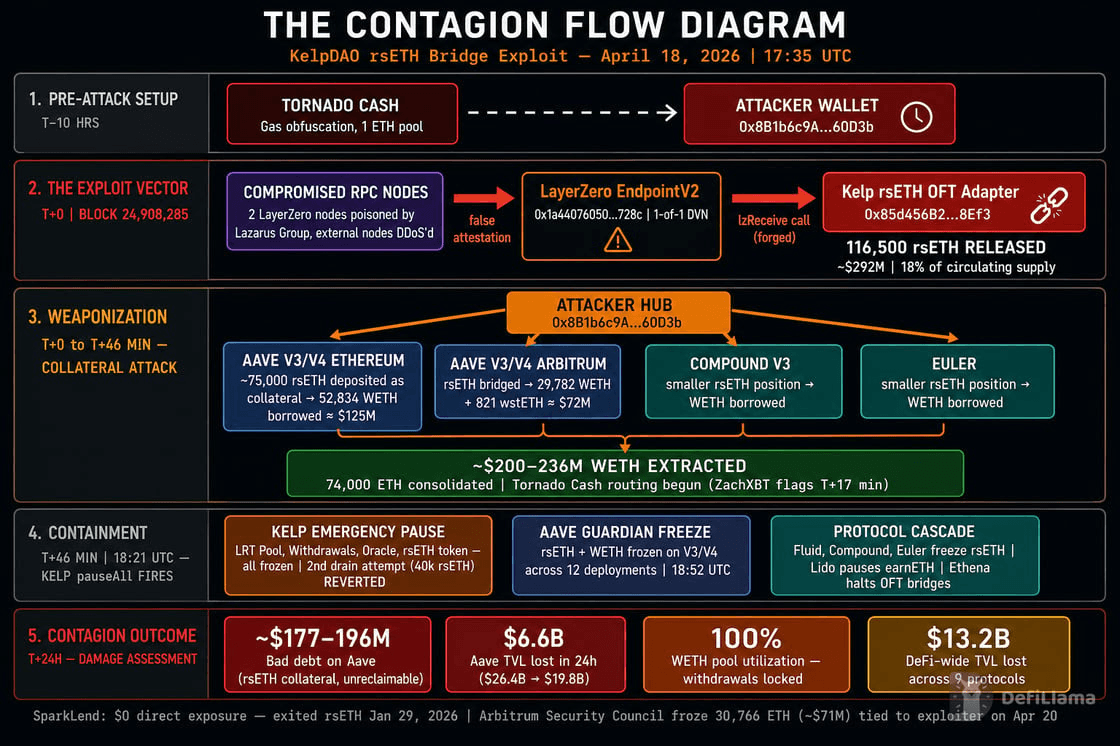
The unauthorized minting of 116,500 rsETH ($292 million) on April 18 triggered a cascading liquidity crisis across major EVM lending markets, serving as a brutal stress test for institutional allocators. This event ruthlessly exposed the double-edged nature of DeFi composability, demonstrating how a localized infrastructure failure in a cross-chain bridge can instantaneously synthesize a systemic contagion event. While the initial exploit occurred at the oracle verification layer, the true damage was inflicted entirely downstream as unbacked synthetic assets infiltrated primary money markets.
The velocity of the contagion was entirely a byproduct of permissionless integration. Once the attackers bypassed the 1-of-1 Decentralized Verifier Network (DVN) and minted the fraudulent rsETH, they did not attempt to swap it on decentralized exchanges, which would have incurred massive slippage and alerted MEV bots. Instead, within a 45-minute window, the attacker systematically deposited over 107,000 unbacked rsETH into lending protocols, weaponizing the asset's established 1:1 oracle peg to Ethereum.
Source: DefiLlama
The Collateral Drain: By posting the fraudulent rsETH as pristine collateral, the attackers were able to borrow heavily against it, draining an estimated $190 million in WETH, USDC, and USDT across Ethereum and Arbitrum.
Bad Debt Synthesis: Because the rsETH had no actual ETH backing it on the Kelp DAO source chain, the attacker effectively swapped worthless synthetic tokens for hard, institutional-grade liquidity, leaving the lending protocols holding the bag.
Secondary Market Arbitrage: As rumors of the unbacked supply spread, arbitrageurs began shorting rsETH on secondary DEXs, threatening to violently break the peg and trigger mass liquidations of legitimate user positions across all integrated protocols.
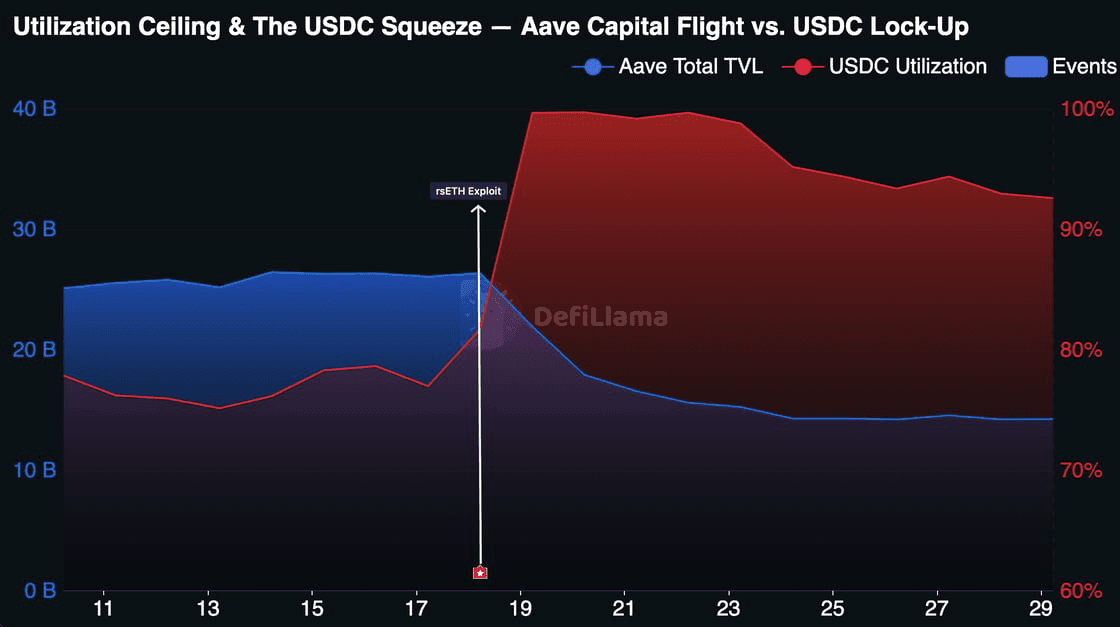
Aave V3 absorbed the brunt of this systemic shock, taking on between $123 million and $150 million in instantaneous bad debt. The immediate consequence was a severe liquidity crunch that paralyzed the market. As institutional lenders identified the toxic collateral entering the system, a bank run ensued. Legitimate depositors rushed to pull their capital from Aave, resulting in a staggering ~$10 billion capital flight over just 72 hours.
This mass exodus triggered the protocol's automated risk parameters, causing utilization rates in the USDC and WETH pools to spike to a rigid 100%. At this utilization ceiling, withdrawal functions structurally fail because the liquidity pools are completely exhausted. Borrowing APRs dynamically surged above 85% in a frantic, automated bid to attract fresh capital, but with toxic collateral sitting on the balance sheet, the market remained entirely frozen.
Source: DefiLlama
The contagion was only contained by the unprecedented, coordinated intervention of "DeFi United." Recognizing that a permanent rsETH depeg would trigger a multi-protocol liquidation death spiral, a consortium including Consensys, Aave DAO, and Lido rapidly pledged $303 million (132,650 ETH). This capital wall ring-fenced the compromised lending markets, explicitly absorbing the bad debt and allowing protocols to safely freeze their rsETH markets without punishing legitimate liquidity providers.
Summary
The Kelp DAO contagion illustrates that in a highly composable DeFi ecosystem, tail risks are shared network-wide. A single point of failure in a cross-chain verifier allowed attackers to synthesize collateral and paralyze the industry's deepest lending markets within an hour, forcing a $303 million centralized bailout to prevent systemic collapse.
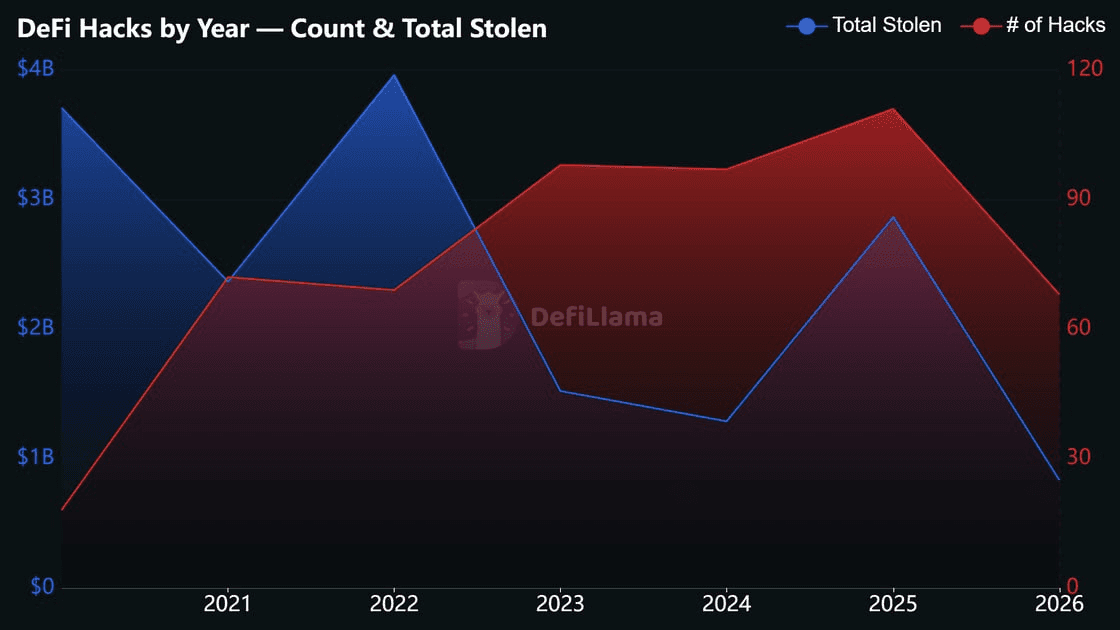
Access Control: DeFi's Trending Risk
In the first four months of 2026, 68 DeFi exploits have already been recorded. At that pace, the year is on track for roughly 200 incidents, compared with 111 in 2025 and an annual average of about 85 across 2021 through 2024. The average loss per exploit has not moved in lockstep with the count. Across 2026 year to date, the mean loss sits at approximately $12 million per incident, in line with 2023 ($15M) and 2024 ($13M) and well below the 2025 average of around $26 million. The salient observation is less that individual hacks are getting larger and more that hacks are occurring more frequently, with the distribution of losses inside that bucket becoming highly uneven.
Source: DefiLlama
Within those losses, the concentration by category is the more material observation. Access control failures, including stolen private keys, compromised multisigs, and mismanaged admin roles, have consistently accounted for a larger share of capital lost than of incident count. From 2021 through 2024, access control represented roughly a quarter to a third of all hacks while producing between 50 and 66 percent of total dollars stolen. 2026 year to date is the most lopsided reading on record: access control accounts for under 18 percent of incidents but more than 80 percent of every dollar lost. The implied average loss for an access control incident this year is several multiples of any other category, and the gap has widened rather than narrowed.
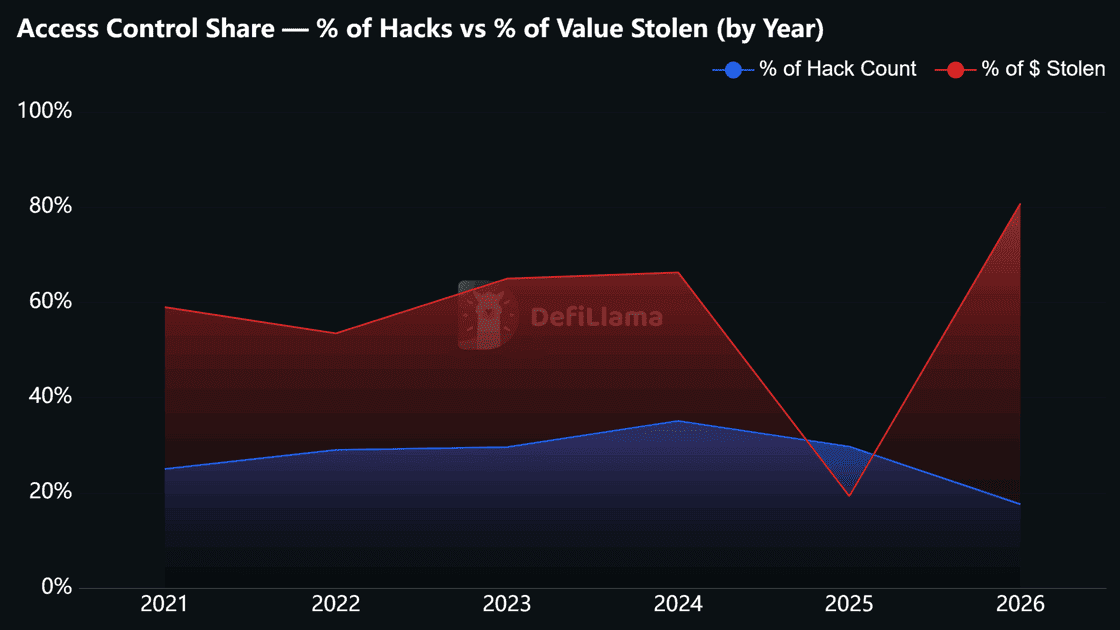
Source: DefiLlama
The structural pressure on this trend is likely to intensify. AI tooling has lowered the cost of scanning code, fuzzing dependencies, and surfacing previously latent attack vectors. Work that once required an expert auditor weeks of effort can now be probed continuously and at scale by anyone with a model and an API key. Defenders have access to the same tools, but offense and defense do not benefit symmetrically. An attacker needs to find only one viable path, while a protocol must close every one. As model capability improves, the marginal cost of discovery falls, and the long tail of bugs and operational gaps that are economically un-auditable today becomes more accessible to opportunistic actors.
That dynamic places redundancy at the access layer at the center of any practical security posture. Once a key is compromised or a privileged function is reached, the speed and finality of on-chain settlement convert what would be a containable incident in traditional finance into a total loss event. The standard mitigations are well understood. They include multi-party signing with meaningful quorums, role separation between operational and privileged functions, timelocks on actions that can move user funds or alter critical parameters, and circuit breakers that throttle outflows when activity diverges from baseline. None of these measures prevent every exploit. Their function is to create time between compromise and full drain, and time is the one resource that pure on-chain settlement does not otherwise provide.
The data trajectory is consistent. Hack frequency is rising, and access control is taking an outsized share of the dollar damage, with 2026 year to date marking the most lopsided ratio observed in the data. Combined with a step change in attacker tooling, the operating environment increasingly favors protocols that have assumed compromise will eventually occur and engineered the blast radius down to a recoverable size.






