
Aave v4 Launches Modular Lending
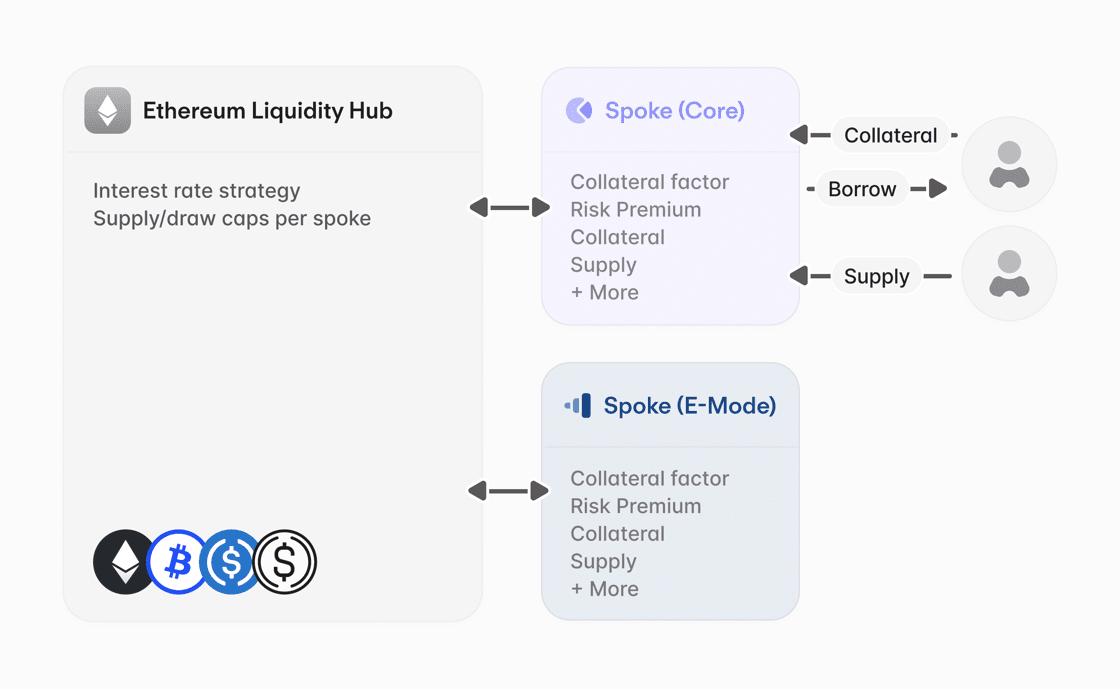
Aave v4 introduces a fundamental re-engineering of the protocol's lending logic, moving from isolated pools to a system that decouples asset storage from risk management. This Hub and Spoke model is designed to eliminate liquidity fragmentation and introduce granular risk pricing, providing a more scalable infrastructure for institutional and retail capital.
V4 introduces Liquidity Hubs and Spokes as core concepts in the architecture. The Liquidity Hubs act as a unified liquidity layer for multiple Spokes to draw from, enabling access to deeper liquidity. Spokes introduce isolated entry points with specific risk parameter settings adapted to the assets in the spoke.
Source: Aave
This structural shift enables risk premiums to be included on top of the base borrow rate for the same asset. The premiums are dynamic and adjust based on the volatility and liquidity of the pledged collateral. By charging higher rates for riskier assets, the protocol ensures lenders are compensated for tail-risk while allowing high-quality collateral to incur minimal premiums.
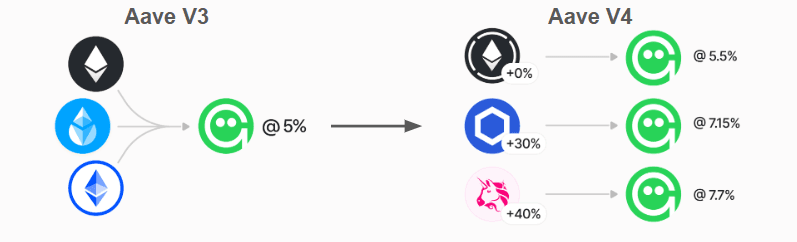
Source: Aave
To enhance protocol stability and reduce borrower equity loss, the v4 Liquidation Engine replaces binary liquidations with a more refined mechanism:
Target Health Factor: Liquidators can only repay the minimum debt required to return a position to a predefined health factor. This prevents over-liquidation during temporary market volatility.
Variable Bonuses: V4 utilizes a Dutch-auction mechanism where the bonus paid to liquidators increases as a position's health factor declines.
More flexible and dynamic liquidation parameters will become increasingly important in the shift to RWAs where atomic liquidations are less reliable and sophisticated liquidators will need to assess duration risk when executing liquidations.
Aave v4 joins the transition toward modular money markets that decouple the liquidity layer from the access layer. As more institutions onboard into DeFi, bespoke parameterizations of entry points to match risk profiles and regulatory requirements is increasingly important. Designs such as Aave v4’s hub and spoke model will become more important to meet the needs of institutions.
Key Weekly DeFi Metrics
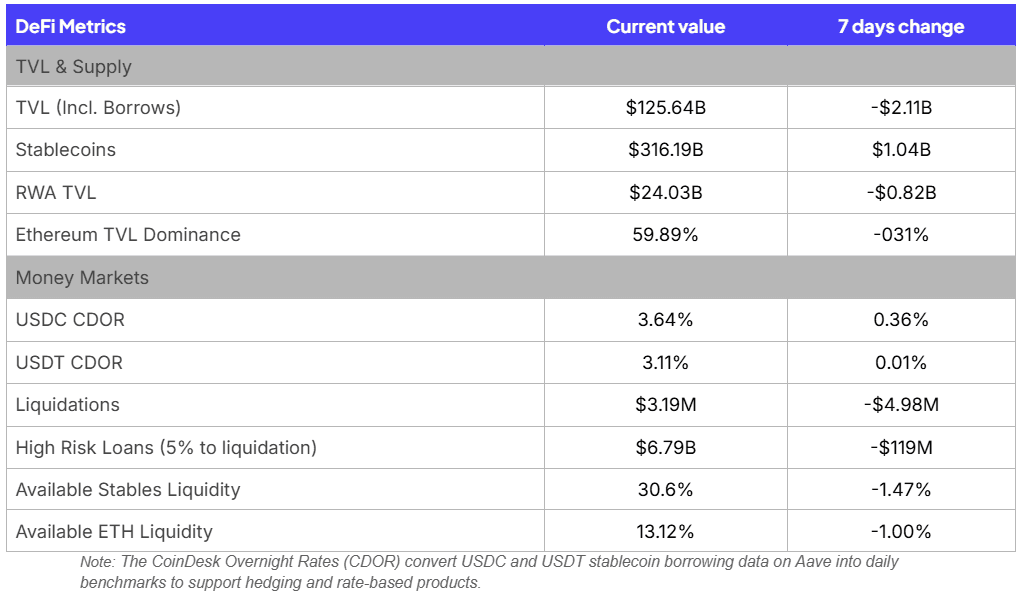
Key takeaways for this week:
Metrics are relatively flat as macro risks continue to prevail. The $2B drop in TVL can be attributed to contagion effect of the Drift exploit
Ethereum dominance has not budged even with the Drift exploit, suggesting the TVL drop happened across multiple chains as larger users derisked across all of DeFi
The Architecture of Trust: Advancing On-Chain Verification of OpSec in DeFi
Recent security incidents involving the Resolv and Drift protocols have identified a significant gap in DeFi operational security. While these protocols maintained high standards for smart contract audits, they suffered from failures in off-chain infrastructure, specifically regarding cloud-based signing keys and administrative access management. These cases demonstrate that protocol security depends not only on immutable code but also on the mutable administrative processes that manage it.
The interface between blockchain protocols and off-chain operational management represents a primary attack surface. While tools like timelocks and circuit breakers are transparently deployed on-chain, they fail to capture the security status of the off-chain environments that trigger them. Current operational actions are often managed through private dashboards, leaving the integrity of signing environments and key management unverifiable to external parties. Establishing a more resilient framework requires transitioning these off-chain metrics into a public, verifiable format through institutional-grade attestations.
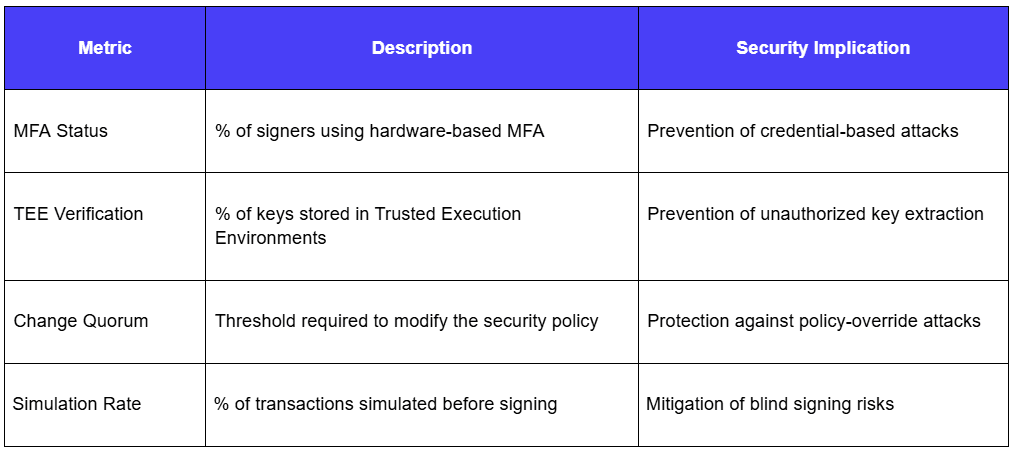
On-Chain Security Verification and Metrics
As an example, the Ethereum Attestation Service provides a framework for institutional providers to publish cryptographically signed claims regarding a protocol's security configuration. Tools such as Fireblocks Security Posture Management and the Squads AUDIT_MULTISIG_SECURITY feature can serve as the technical foundation for these claims, scanning for risky settings like missing IP allowlists or unrotated API keys. By exposing this data through EAS, the ecosystem can develop a ratings and alerts system derived from verifiable on-chain and off-chain metrics.
The following table details metrics that could form the basis of a standardized on-chain operational security report.
Automated Risk Mitigation and Contagion Prevention
The primary application of this verification framework is the implementation of automated, programmatic defenses. Rather than relying on manual intervention, a degradation in security scores or the detection of unauthorized configuration changes can trigger on-chain circuit breakers. In such scenarios, integrated platforms could automatically pause markets or offboard specific collateral types to prevent the secondary contagion effects observed in previous incidents. By shifting from trust-based assumptions to cryptographic verification, the DeFi ecosystem can achieve a more standardized and resilient financial infrastructure.






